My first keysigning party
 I was to my first keysigning party today, arranged by Diana Senn
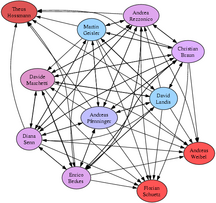
in the System Security course at [ETH][]. The results so far can
be seen in the graph on the right, click for a full-sized image.
I was to my first keysigning party today, arranged by Diana Senn
in the System Security course at [ETH][]. The results so far can
be seen in the graph on the right, click for a full-sized image.
The keysigning itself was quite amusing. First we each got a list with the fingerprints of all the keys involved. The list was checked by having each of us read aloud the fingerprint we had brought along. For a random guy it must have been a strange thing to witness: ten geeks each reading their string of forty hexadecimal digits aloud one after another… :-)
The fun continued with the identity check. We lined up in a row and the first guy went past us and checked our IDs along the way. That was it — everybody had proper ID and everything matched.
Coming home I signed peoples keys — if a key had multiple User IDs, then I signed each ID separately. I then sent the signatures on each User ID to the corresponding email address in encrypted mails. This ensures that my signatures wont end up on User IDs which the owner of the private key doesn’t control.
The problem is that anybody can make a user ID with, say, “Martin Geisler — mgeisler@mgeisler.net” as the user information. But if they don’t control that address, then they wont get the signatures sent to it. And if the recipient doesn’t control the secret key, then the encrypted signature is useless to him. So this step binds the email addresses to the key, and should be done if one feels paranoid — or if one want to try and be a crypto-nerd :-)
Martin Geisler:
Updated with signatures from David Landis.
10 June 2005, 9:16 pmMartin Geisler:
The graph has been updated with the latest signatures from the weekend.
13 June 2005, 7:53 amMartin Geisler:
The graph has been updated once again — everybody now has at least five signatures on their key, so I think the keyparty was quite succesful.
By the way: one can find more paths connecting keys at the PGP Pathfinder.
16 June 2005, 1:03 pmJanus’ Weblog » Blog Archive » Evening in November:
[...] Martin’s blog has been quite active in the mean time. Apparently they have a lot of free-time in Switcherland. Recently he attended a PGP key-signing party and it seems that me and Thomas have become part of the “strong set”. Not sure exactly what this means - but at least it is obvious that a lot of people will now trust my pgp keys (which just reminded me that I have to link them from the blog) because of the inferred trust. [...]
27 June 2005, 5:48 pm